Microsoft has introduced one of the most strategically important governance capabilities in recent years for Microsoft 365 environments: Unified Tenant Configuration Management (UTCM).
At first glance, this may appear to be another configuration or automation feature. In reality, it signals a structural shift in how Microsoft tenants will be governed in the coming years. Governance is moving away from periodic configuration reviews towards continuous configuration assurance as a core operational control within the Microsoft cloud.
For organisations focused on Microsoft security, compliance and NIS2 readiness, this is a development worth understanding early.
Microsoft 365 governance still has a structural gap
Most organisations today have defined security baselines, Conditional Access strategies and governance frameworks. Policies exist. Standards exist. Responsibilities are assigned.
However, far fewer organisations can answer the following questions with confidence.
- Is the tenant still aligned with the approved baseline today?
- When did a critical configuration last change?
- Would a weakened security control be detected quickly?
- Can configuration integrity be demonstrated during an audit?
This is the gap between policy governance and runtime governance.
Traditional Microsoft 365 governance relies heavily on periodic reviews, manual checks and point-in-time validation. That model does not scale in a cloud environment where configuration changes can occur continuously across identity, endpoint and data layers.
Unified Tenant Configuration Management is Microsoft’s response to this reality.
Unified Tenant configuration governance is becoming a continuous control, not a periodic review.
Microsoft is productising configuration governance
Unified Tenant Configuration Management, also referred to as unified tenant configuration management in Microsoft Graph preview, introduces a Microsoft-native way to treat tenant configuration as a continuously governed control surface.
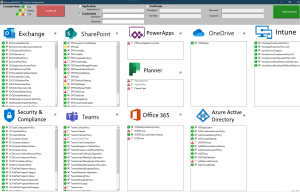
The underlying model is straightforward. Organisations define an approved configuration baseline across core Microsoft workloads such as Microsoft Entra ID, Intune, Microsoft Defender, Microsoft Purview and collaboration services. The platform then enables configuration snapshots, baseline comparison, drift detection and structured remediation workflows.
In practical terms, this also introduces native tenant configuration backup and comparison capabilities.
Microsoft is effectively enabling organisations to capture configuration states, monitor drift against approved baselines and use those snapshots as governance and audit evidence over time.
This moves configuration assurance from custom scripting towards a supported platform capability.
This establishes a define, monitor and correct lifecycle that is embedded into the platform rather than dependent on scripts or manual processes. Microsoft is effectively productising configuration governance for Microsoft 365.
Microsoft’s unified tenant configuration management model is already emerging through Microsoft Graph preview capabilities, where configuration snapshots, monitoring and drift comparison are exposed as native control-plane functions. This indicates that configuration governance is not being positioned as an optional tooling layer, but as a foundational component of the Microsoft 365 platform itself.
Configuration drift is the real operational risk

In practice, most Microsoft cloud security issues do not originate from missing controls. They arise from control drift.
Conditional Access policies are modified during troubleshooting and not restored. Multi-factor authentication requirements are relaxed temporarily. Security settings are changed during incident response. Data protection policies diverge between environments.
Over time, the tenant gradually moves away from its intended security posture. Without structured configuration monitoring, this often remains unnoticed until an audit or incident reveals the deviation.
Tenant Configuration Management introduces the foundation for detecting and managing configuration drift in a structured and repeatable manner.
From scripting discipline to platform capability
Mature Microsoft environments have long relied on configuration-as-code approaches to maintain tenant consistency. We previously explored Microsoft365DSC as a configuration governance and baseline enforcement approach for Microsoft 365 environments. Microsoft is now formalising that philosophy within the platform itself.
Unified Tenant Configuration Management can be viewed as the natural evolution of this model. It moves governance from community-driven scripting towards a Microsoft-native configuration governance capability integrated into the control plane.
The most important change is operational. Tenant configuration governance is becoming a continuous control rather than a periodic project. For security and governance teams, this significantly reduces reliance on custom automation and manual oversight while improving consistency and traceability.
Compliance and audit implications
For organisations operating under NIS2, ISO 27001 or similar frameworks, the ability to demonstrate that controls remain effective over time is becoming increasingly important.
Unified Tenant Configuration Management supports this by enabling baseline definition, configuration monitoring and historical comparison. This allows organisations to demonstrate not only that controls were implemented, but that they are continuously maintained.
Audit preparation for Microsoft environments often involves reactive evidence gathering. Screenshots and manual exports are collected shortly before an audit takes place. With structured configuration snapshots and monitoring, organisations can provide evidence of configuration state, change history and remediation actions in a more structured and defensible manner.
This strengthens both audit readiness and overall governance maturity.
Relevance for NIS2 and operational governance
NIS2 and related regulatory frameworks emphasise demonstrable security governance, continuous monitoring and risk-based control management. Organisations must be able to show that appropriate measures are implemented and maintained.
Unified Tenant Configuration Management supports this expectation by enabling organisations to demonstrate configuration control across identity, endpoint and data protection layers. It improves visibility into unauthorised or risky changes and supports evidence-based governance.
While no single capability ensures regulatory compliance, it provides an important technical foundation for modern Microsoft cloud governance.
Positioning within the Microsoft security architecture
Unified Tenant Configuration Management should not be viewed as another standalone workload. It acts as a governance layer across the Microsoft security and compliance stack, including Entra ID, Intune, Defender and Purview.
Its purpose is to ensure that the configuration of these platforms remains aligned with approved security and compliance baselines over time.
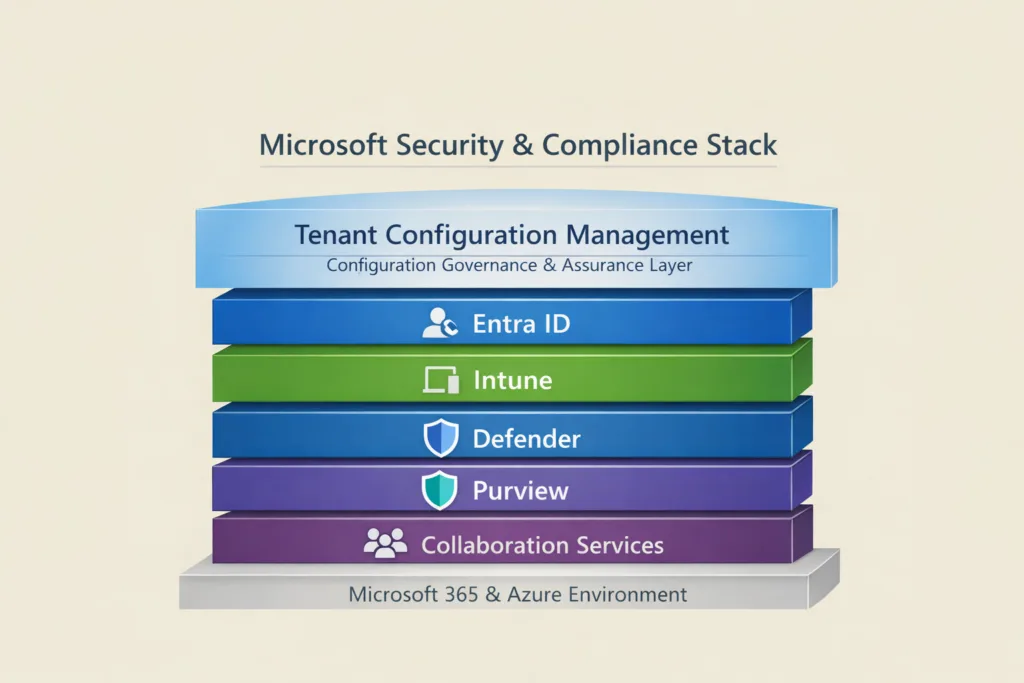
Above this sits Unified Tenant Configuration Management as a configuration governance and assurance layer.
Strategic implications for security and GRC leaders
Unified Tenant Configuration Management provides a clear indication of Microsoft’s direction. Microsoft 365 tenants will increasingly be governed as continuously monitored environments rather than static configurations reviewed periodically.
Security and governance leaders should begin identifying which tenant configurations represent critical controls, what the approved baseline should be and how configuration drift should be detected and managed. Consideration should also be given to how configuration governance integrates with risk management and compliance reporting.
Early adoption will likely begin with pilot scenarios. However, the long-term trajectory is clear. Continuous configuration governance will become a core component of mature Microsoft security operating models.
Final thoughts
Unified Tenant Configuration Management represents more than a new feature. It marks the beginning of a shift towards continuous Microsoft tenant governance.
By enabling configuration baselines, drift detection and structured monitoring, Microsoft is laying the foundation for stronger configuration assurance, improved audit readiness and reduced operational risk.
Not because the concept is entirely new, but because it is now becoming operationally achievable within the Microsoft ecosystem itself.
Expect tenant configuration governance to become a standard control in mature Microsoft environments within the next three to five years.
Related Microsoft identity and security insights:
- Exploring Conditional Access bypass scenarios in Microsoft Entra ID
- Is your guest access configuration in Entra putting your organisation at risk?
- Microsoft365DSC and configuration governance for Microsoft tenants
- Strengthening Microsoft cloud governance and resilience in enterprise environments.
Update : 25 March 2026
Microsoft has now formally positioned tenant governance as a broader multi-tenant control model in Microsoft Entra, combining related tenant discovery, governance relationships, tenant configuration management, and secure tenant creation. This reinforces a broader shift already visible in Microsoft 365 governance: moving from static configuration hardening toward continuous, baseline-driven control across tenant estates. While Tenant Configuration Management APIs are generally available, the broader Tenant Governance experiences are currently in public preview and rolling out. https://techcommunity.microsoft.com/blog/microsoft-entra-blog/microsoft-entra-tenant-governance-secure-and-manage-multi-tenant-environments-at/4462427

