Tag: IT Automation
-

Unified Tenant Configuration Management: Microsoft moves tenant governance into continuous control
Microsoft is introducing Tenant Configuration Management as a native configuration governance layer for Microsoft 365. This article explores how continuous configuration monitoring, drift detection and baseline enforcement will reshape Microsoft security and compliance operating models.
-

Step-by-Step: Build a Copilot Agent for Smarter Intune Alerts in 15 Minutes
Every IT professional knows the struggle: an Intune notification pings with a vague error code or cryptic alert about a device compliance issue, failed update, or potential security threat. You’re left scratching your head, wondering, “What does this even mean?” These unclear messages can bury critical issues, like non-compliant devices or malware risks, in a…
-

How to Enhance Microsoft 365 Auditing: Beyond the Unified Audit Log
Discover how to strengthen your Microsoft 365 auditing strategy in this practical guide. Learn the strengths and limitations of the Unified Audit Log (UAL) and explore actionable steps to go beyond its basics—using Audit (Premium), SIEM integration, PowerShell automation, and more. Perfect for IT professionals aiming to boost security and compliance with advanced auditing techniques.…
-

Automate Your Onboarding and Offboarding in 15 Minutes with Entra Identity Governance
Onboarding and offboarding employees manually can lead to errors, delays, and compliance risks. With Microsoft Entra Identity Governance, you can automate these processes in just 15 minutes—no scripting required. Discover how to streamline user lifecycle management, enhance security, and maintain compliance with Entra’s powerful workflows and customisable extensions. Perfect for organisations looking to save time,…
-
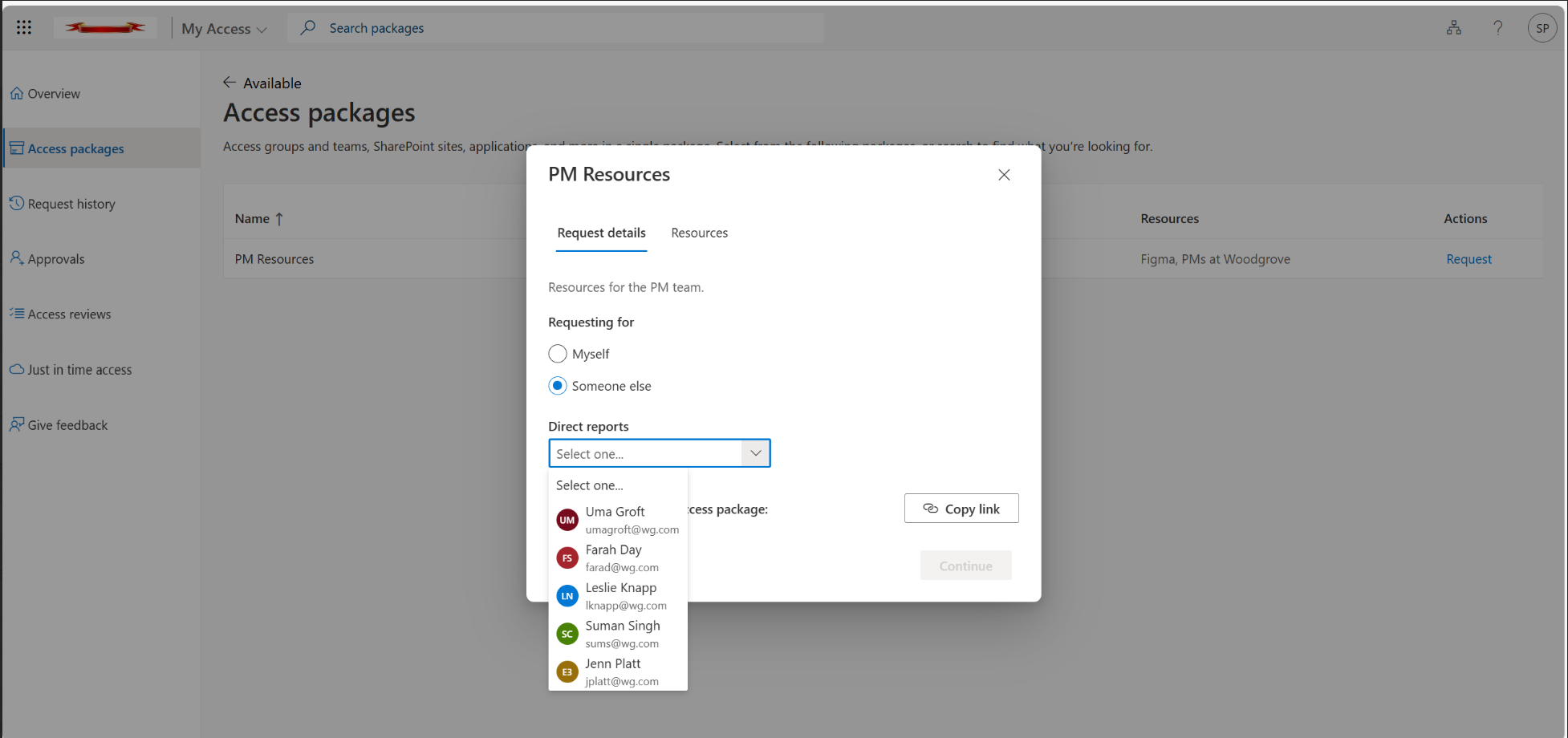
Introducing Microsoft Entra’s “Request on Behalf”: A Better Way to Manage Temporary Access Passes
Discover how Microsoft Azure AD’s new “Request on Behalf” feature revolutionises the management of Temporary Access Passes (TAPs). This feature simplifies access workflows for IT admins and Managed Service Providers (MSPs) by enabling requests to be made on behalf of others, enhancing efficiency, governance, and security across multiple tenants. Learn how to configure and implement…
-
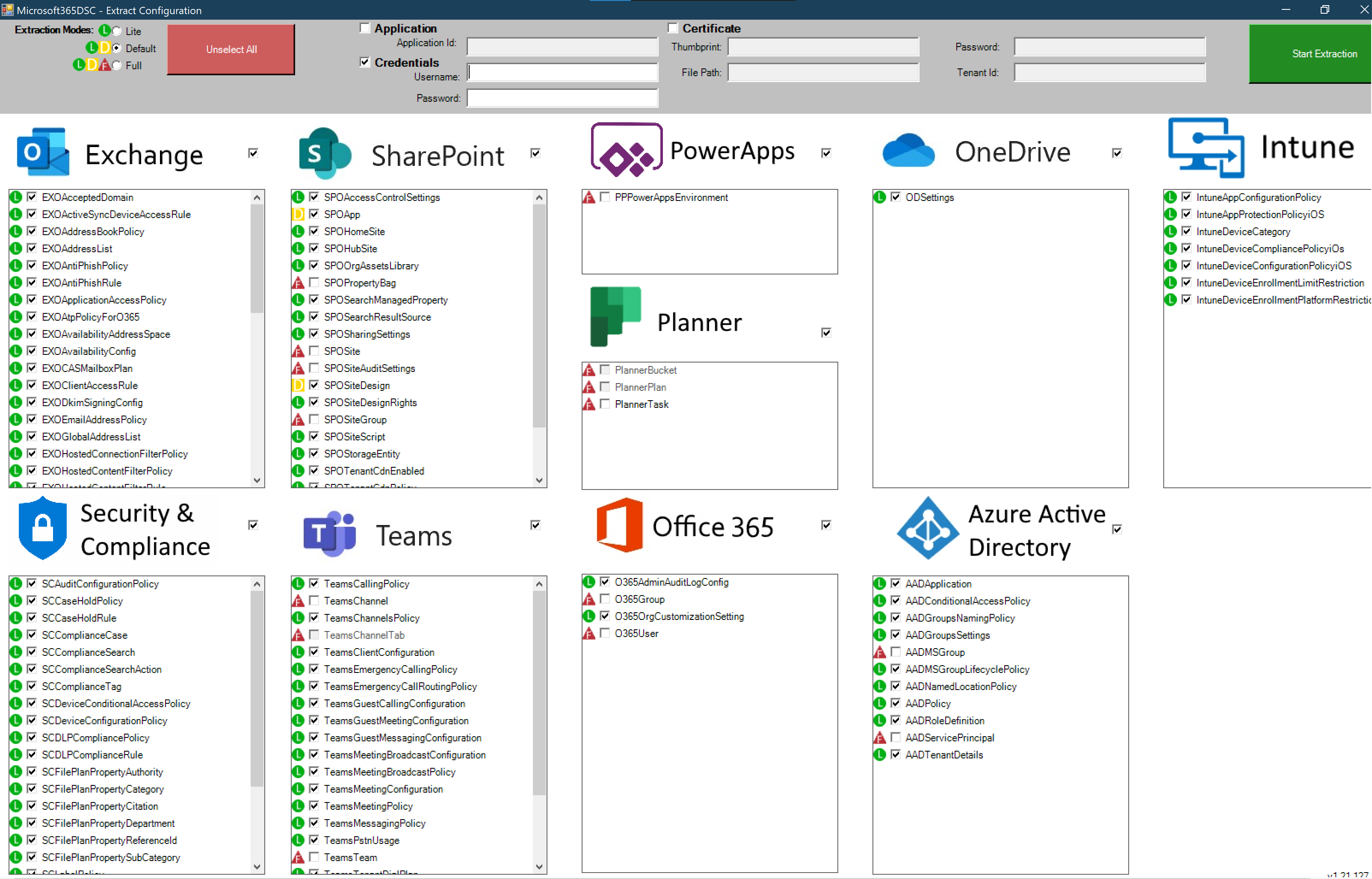
Microsoft 365 DSC: Automate, Configure, and Monitor Like a Pro
Discover how Microsoft 365 Desired State Configuration (DSC) empowers IT professionals to automate, monitor, and maintain tenant configurations with ease. This blog dives into the benefits of DSC, including drift prevention and multi-tenant synchronization, while providing a step-by-step guide for deployment. Learn from real-life examples covering Exchange Online, Intune, and Entra, and explore additional resources…
-

Unlocking DUDE: A Guide to Dynamic User and Device Enumeration
DUDE (Dynamic User and Device Enumeration) is a powerful tool for IT administrators to automate the process of retrieving and managing user and device data from Azure AD. Leveraging Microsoft Graph API and PowerShell, DUDE streamlines security monitoring, compliance reporting, and device management. This guide covers its architecture, setup, common use cases, and real-world applications…