Tag: Data Protection
-

Require Risk Remediation: The Game-Changer for Conditional Access Policies
Discover the game-changing ‘Require Risk Remediation’ control in Microsoft Entra Conditional Access. This preview feature simplifies risk management by handling both password and passwordless users in one policy, reducing complexity and misconfigurations. Get a step-by-step guide, real-world benefits, and pragmatic insights into its limitations for enhanced security.
-

Is Your Guest Access in Entra Putting Your Organisation at Risk?
Many organisations assume Microsoft Entra ID handles guest users securely by default—but it doesn’t. In this post, we uncover the top 5 common mistakes in guest access management, from excessive directory visibility to perpetual access without lifecycle controls. Learn how to lock down your tenant with practical fixes, ensuring secure B2B collaboration without the risks.
-

Step-by-Step: Build a Copilot Agent for Smarter Intune Alerts in 15 Minutes
Every IT professional knows the struggle: an Intune notification pings with a vague error code or cryptic alert about a device compliance issue, failed update, or potential security threat. You’re left scratching your head, wondering, “What does this even mean?” These unclear messages can bury critical issues, like non-compliant devices or malware risks, in a…
-

New OneDrive Feature Poses Data Leak Risk for Businesses
Microsoft’s new OneDrive feature, launching in May 2025, lets users sync personal accounts on work devices—a convenience that could spell trouble for businesses. This opens the door to data leaks and compliance risks. Our post dives into these security concerns and offers IT administrators practical solutions using Group Policies and Intune. Learn how to lock…
-

AI Governance in 2025: Protecting Against Data Exfiltration
As Artificial Intelligence (AI) transforms industries with unparalleled innovation, it also brings serious security risks like data leaks and malicious attacks. A staggering 57% of organisations report rising AI-related incidents, yet 60% lack basic controls. This blog explores the top AI threats, including data exfiltration and malicious prompt injection, and outlines a Zero Trust framework…
-

How to Enhance Microsoft 365 Auditing: Beyond the Unified Audit Log
Discover how to strengthen your Microsoft 365 auditing strategy in this practical guide. Learn the strengths and limitations of the Unified Audit Log (UAL) and explore actionable steps to go beyond its basics—using Audit (Premium), SIEM integration, PowerShell automation, and more. Perfect for IT professionals aiming to boost security and compliance with advanced auditing techniques.…
-

Master SharePoint Version History: Your Ultimate Guide to Limits, Storage, and Security
Take control of SharePoint version history! This guide shows you how to set limits, cut storage (e.g., 1TB to 106GB), and enhance security for NIS2 compliance with easy steps and PowerShell tips. Optimize your site now—read on!
-

Strengthening Cloud Governance and Resilience with Microsoft
Effective cloud governance is critical in today’s digital landscape. Organisations must tackle risks, ensure compliance, and design resilient architectures to meet directives like NIS2. This guide outlines six essential steps to achieve robust cloud governance using Microsoft tools like Azure Service Health, Microsoft Defender for Cloud, and Azure Backup. From mitigating concentration risks to preparing…
-
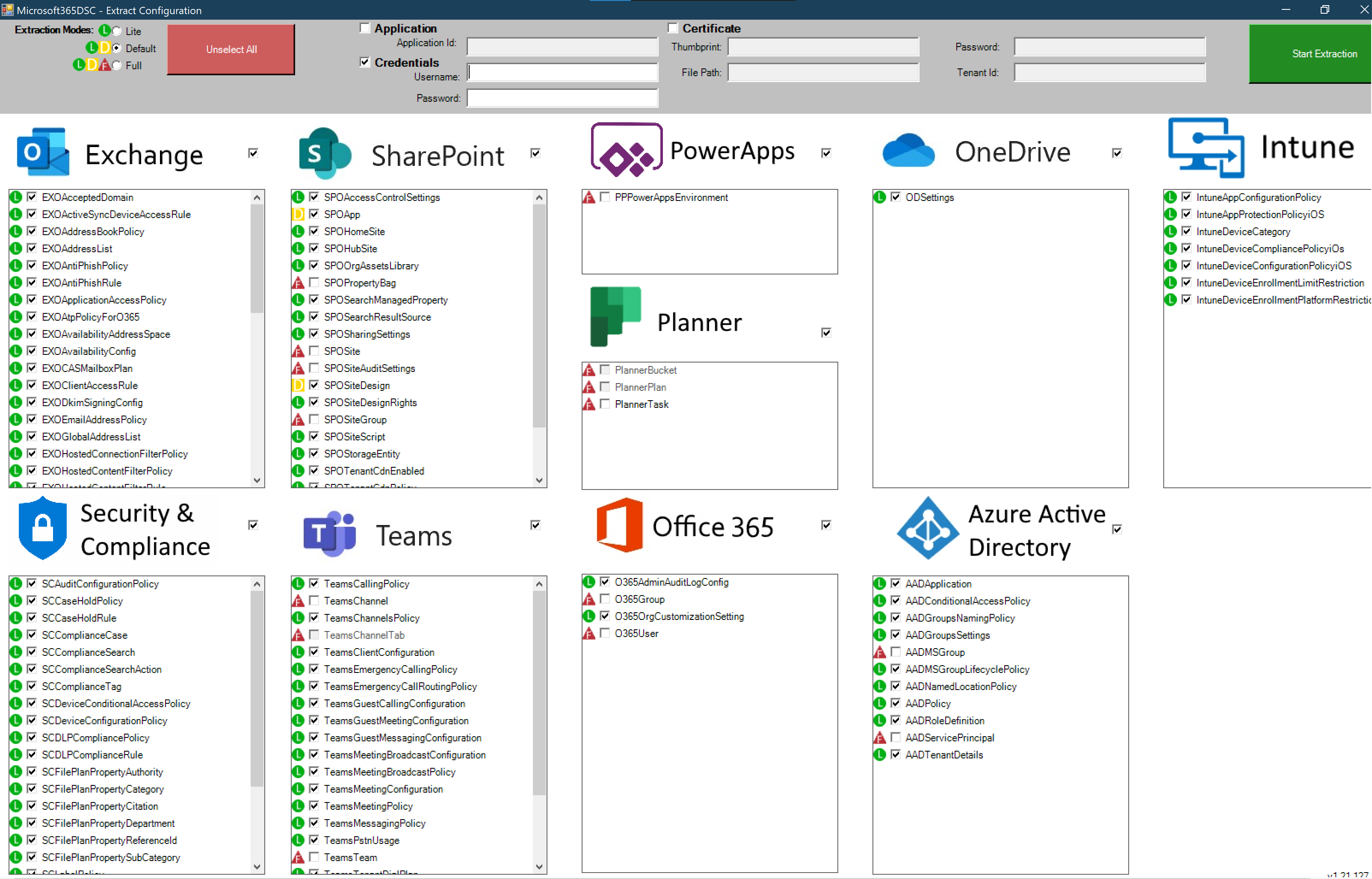
Microsoft 365 DSC: Automate, Configure, and Monitor Like a Pro
Discover how Microsoft 365 Desired State Configuration (DSC) empowers IT professionals to automate, monitor, and maintain tenant configurations with ease. This blog dives into the benefits of DSC, including drift prevention and multi-tenant synchronization, while providing a step-by-step guide for deployment. Learn from real-life examples covering Exchange Online, Intune, and Entra, and explore additional resources…