Category: Entra & Identity
-

Microsoft Dumps OTP Authentication for SharePoint Online Sharing with Entra ID B2B
Microsoft is phasing out One-Time Passcode (OTP) authentication for SharePoint Online and OneDrive external sharing, replacing it with Entra ID B2B Collaboration, effective July 1, 2025 (MC1089315). Legacy OTP links will stop working, requiring users to re-share content to restore access for external collaborators, who must also register for mandatory MFA. Prepare now by notifying…
-

OneDrive File Picker Vulnerability: What You Need to Know
A critical flaw in Microsoft’s OneDrive File Picker could allow third-party apps to access files across Microsoft 365 tenants without user interaction. Learn what happened, the risks involved, and how your organisation can stay protected.
-

New OneDrive Feature Poses Data Leak Risk for Businesses
Microsoft’s new OneDrive feature, launching in May 2025, lets users sync personal accounts on work devices—a convenience that could spell trouble for businesses. This opens the door to data leaks and compliance risks. Our post dives into these security concerns and offers IT administrators practical solutions using Group Policies and Intune. Learn how to lock…
-

AI Governance in 2025: Protecting Against Data Exfiltration
As Artificial Intelligence (AI) transforms industries with unparalleled innovation, it also brings serious security risks like data leaks and malicious attacks. A staggering 57% of organisations report rising AI-related incidents, yet 60% lack basic controls. This blog explores the top AI threats, including data exfiltration and malicious prompt injection, and outlines a Zero Trust framework…
-

How to Enhance Microsoft 365 Auditing: Beyond the Unified Audit Log
Discover how to strengthen your Microsoft 365 auditing strategy in this practical guide. Learn the strengths and limitations of the Unified Audit Log (UAL) and explore actionable steps to go beyond its basics—using Audit (Premium), SIEM integration, PowerShell automation, and more. Perfect for IT professionals aiming to boost security and compliance with advanced auditing techniques.…
-
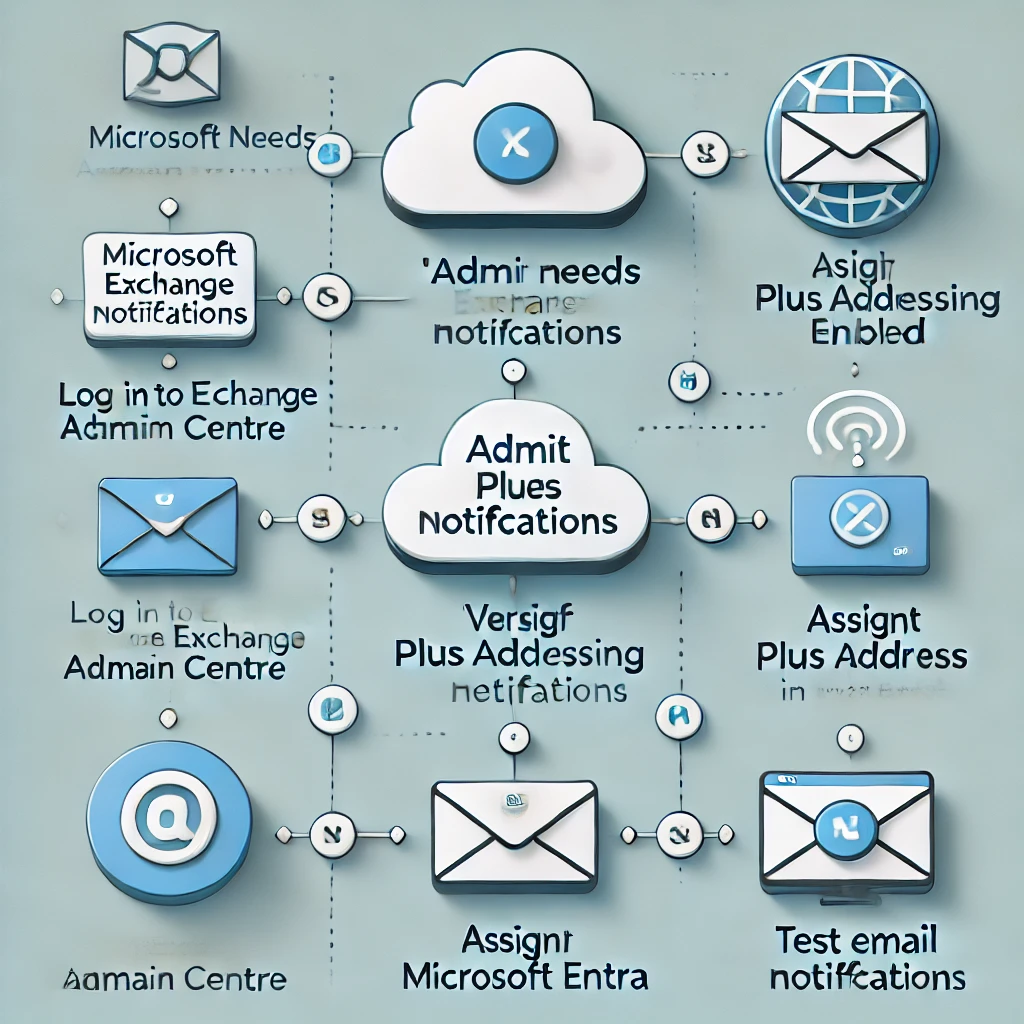
How to Receive Admin Notifications in Microsoft Entra Without a Mailbox
In this blog post, we explore how to receive admin email notifications in Microsoft Entra without assigning mailbox licenses to admin accounts. By leveraging plus addressing in Exchange Online, organisations can route notifications to existing mailboxes, maintaining security and reducing licensing costs. Plus addressing allows admins to create unique email aliases by appending a “+”…
-

Automate Your Onboarding and Offboarding in 15 Minutes with Entra Identity Governance
Onboarding and offboarding employees manually can lead to errors, delays, and compliance risks. With Microsoft Entra Identity Governance, you can automate these processes in just 15 minutes—no scripting required. Discover how to streamline user lifecycle management, enhance security, and maintain compliance with Entra’s powerful workflows and customisable extensions. Perfect for organisations looking to save time,…
-

Strengthening Cloud Governance and Resilience with Microsoft
Effective cloud governance is critical in today’s digital landscape. Organisations must tackle risks, ensure compliance, and design resilient architectures to meet directives like NIS2. This guide outlines six essential steps to achieve robust cloud governance using Microsoft tools like Azure Service Health, Microsoft Defender for Cloud, and Azure Backup. From mitigating concentration risks to preparing…
-
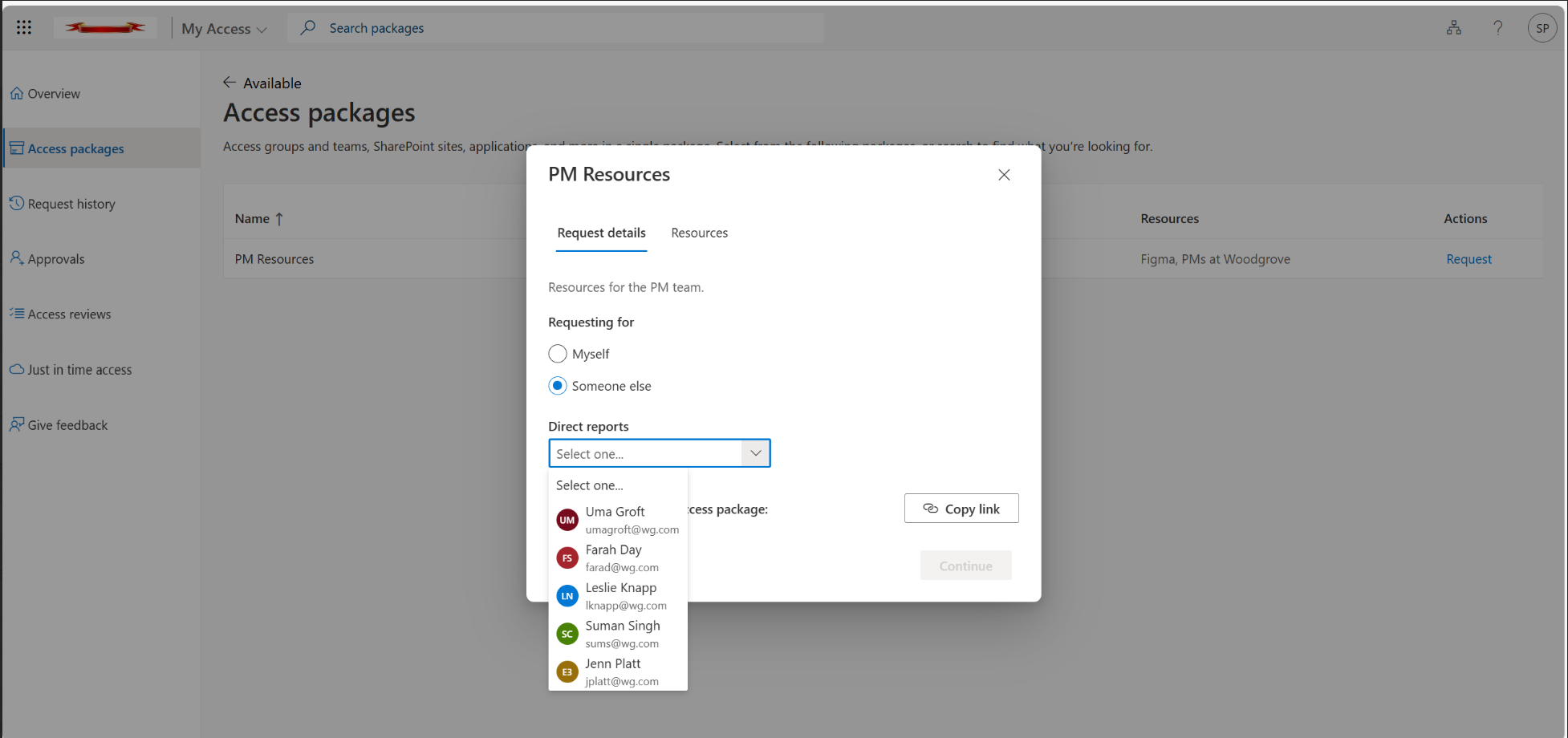
Introducing Microsoft Entra’s “Request on Behalf”: A Better Way to Manage Temporary Access Passes
Discover how Microsoft Azure AD’s new “Request on Behalf” feature revolutionises the management of Temporary Access Passes (TAPs). This feature simplifies access workflows for IT admins and Managed Service Providers (MSPs) by enabling requests to be made on behalf of others, enhancing efficiency, governance, and security across multiple tenants. Learn how to configure and implement…