Tag: PowerShell Automation
-

Is Your Guest Access in Entra Putting Your Organisation at Risk?
Many organisations assume Microsoft Entra ID handles guest users securely by default—but it doesn’t. In this post, we uncover the top 5 common mistakes in guest access management, from excessive directory visibility to perpetual access without lifecycle controls. Learn how to lock down your tenant with practical fixes, ensuring secure B2B collaboration without the risks.
-

How to Enhance Microsoft 365 Auditing: Beyond the Unified Audit Log
Discover how to strengthen your Microsoft 365 auditing strategy in this practical guide. Learn the strengths and limitations of the Unified Audit Log (UAL) and explore actionable steps to go beyond its basics—using Audit (Premium), SIEM integration, PowerShell automation, and more. Perfect for IT professionals aiming to boost security and compliance with advanced auditing techniques.…
-

Master SharePoint Version History: Your Ultimate Guide to Limits, Storage, and Security
Take control of SharePoint version history! This guide shows you how to set limits, cut storage (e.g., 1TB to 106GB), and enhance security for NIS2 compliance with easy steps and PowerShell tips. Optimize your site now—read on!
-
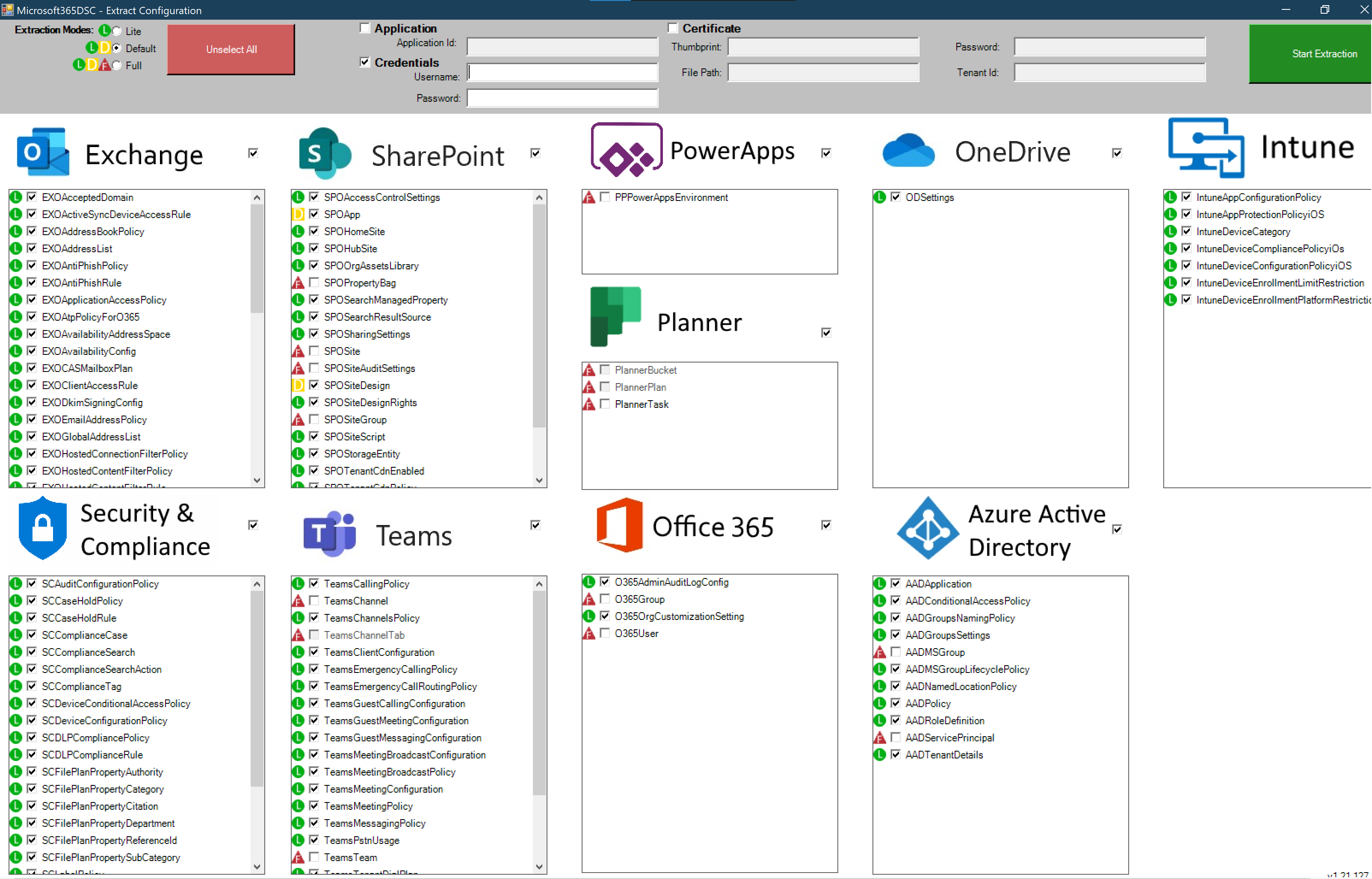
Microsoft 365 DSC: Automate, Configure, and Monitor Like a Pro
Discover how Microsoft 365 Desired State Configuration (DSC) empowers IT professionals to automate, monitor, and maintain tenant configurations with ease. This blog dives into the benefits of DSC, including drift prevention and multi-tenant synchronization, while providing a step-by-step guide for deployment. Learn from real-life examples covering Exchange Online, Intune, and Entra, and explore additional resources…
-

Unlocking DUDE: A Guide to Dynamic User and Device Enumeration
DUDE (Dynamic User and Device Enumeration) is a powerful tool for IT administrators to automate the process of retrieving and managing user and device data from Azure AD. Leveraging Microsoft Graph API and PowerShell, DUDE streamlines security monitoring, compliance reporting, and device management. This guide covers its architecture, setup, common use cases, and real-world applications…
