Author: Driek Desmet
-
Key Updates to OneDrive Retention Policies: What You Need to Know
Microsoft is updating OneDrive retention policies starting 27 January 2025, offering organisations more flexibility while addressing compliance needs and storage concerns. Learn what’s changing, why, and how to prepare
-

Microsoft Tech Insights: Weekly Update #01.2025
Microsoft has made significant strides this week, from expanding its AI ecosystem with models beyond OpenAI for 365 Copilot to a massive $80 billion investment in AI data centers. Wedbush also predicts a 25% tech growth in 2025 led by Microsoft and Nvidia, signaling a transformative era for AI in our industry.
-

Automate Your Onboarding and Offboarding in 15 Minutes with Entra Identity Governance
Onboarding and offboarding employees manually can lead to errors, delays, and compliance risks. With Microsoft Entra Identity Governance, you can automate these processes in just 15 minutes—no scripting required. Discover how to streamline user lifecycle management, enhance security, and maintain compliance with Entra’s powerful workflows and customisable extensions. Perfect for organisations looking to save time,…
-
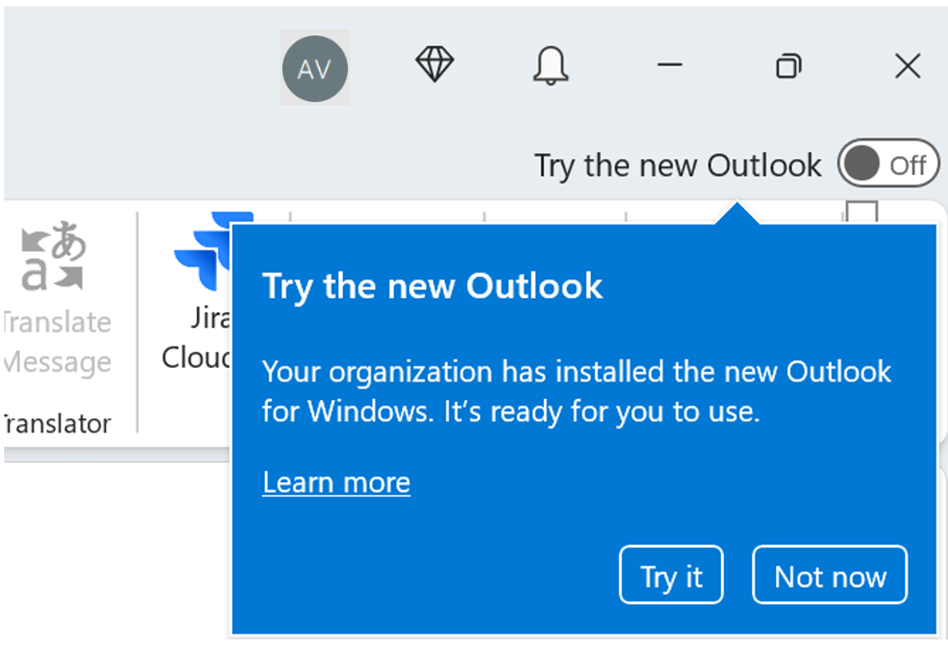
Get Ready: Microsoft Will Automatically Switch to the New Outlook for Windows in 2025!
Microsoft is rolling out the New Outlook for Windows, with automatic transitions starting in January 2025 for Microsoft 365 Business Standard and Premium users, and April 2026 for Enterprise users. Organisations can manage this migration using Microsoft Intune, leveraging detection and remediation scripts to control when and how users switch. Get ahead of the change…
-

Strengthening Cloud Governance and Resilience with Microsoft
Effective cloud governance is critical in today’s digital landscape. Organisations must tackle risks, ensure compliance, and design resilient architectures to meet directives like NIS2. This guide outlines six essential steps to achieve robust cloud governance using Microsoft tools like Azure Service Health, Microsoft Defender for Cloud, and Azure Backup. From mitigating concentration risks to preparing…
-
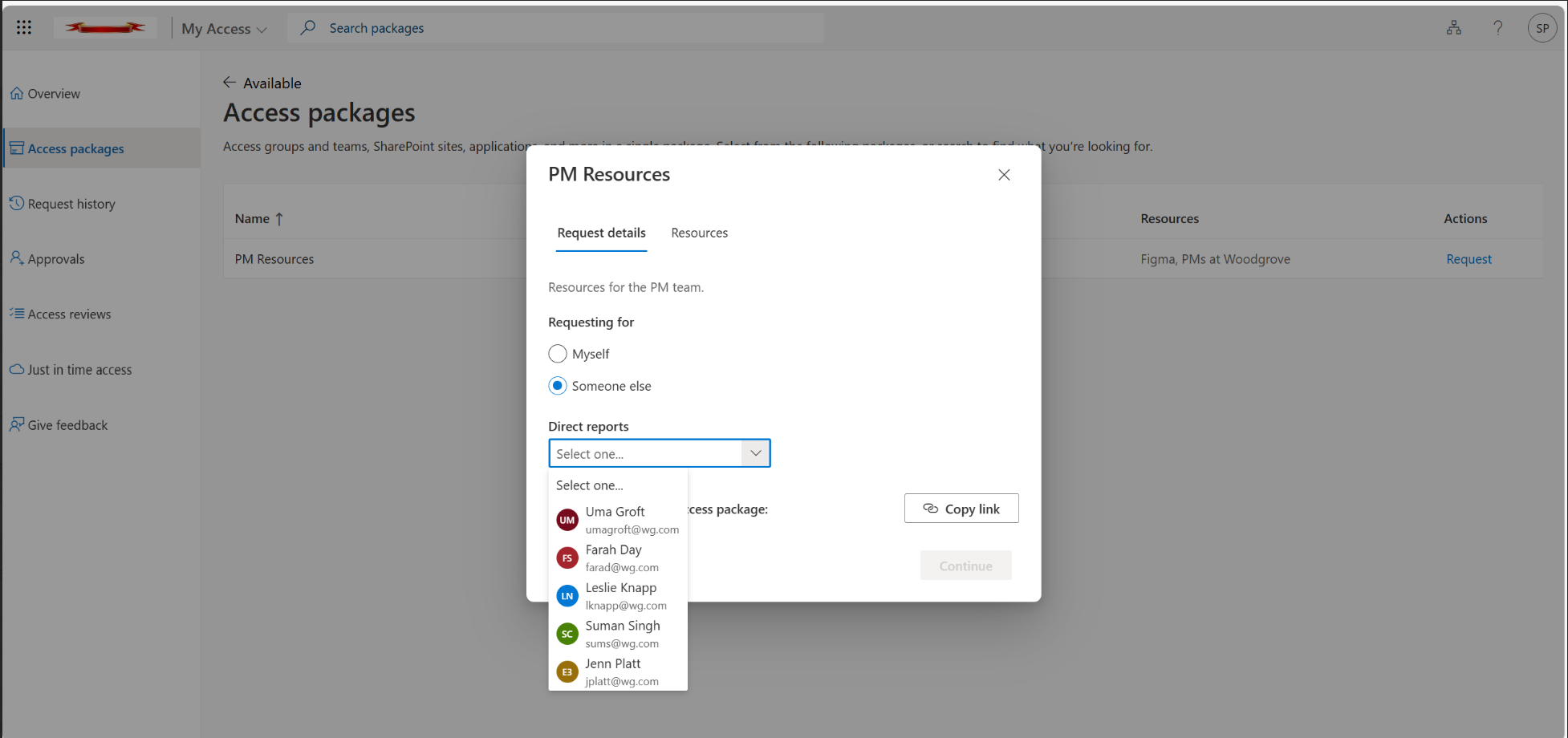
Introducing Microsoft Entra’s “Request on Behalf”: A Better Way to Manage Temporary Access Passes
Discover how Microsoft Azure AD’s new “Request on Behalf” feature revolutionises the management of Temporary Access Passes (TAPs). This feature simplifies access workflows for IT admins and Managed Service Providers (MSPs) by enabling requests to be made on behalf of others, enhancing efficiency, governance, and security across multiple tenants. Learn how to configure and implement…
-

Why Password Policies Matter and How Often to Update Them
In today’s digital age, securing online accounts goes beyond just choosing a strong password. Frequent password changes, once seen as a key security measure, may actually do more harm than good. This blog explores the latest insights from NIST and Microsoft, highlighting why password policies should focus on long, complex passwords and multi-factor authentication (MFA)…
-

My Top 10 Picks from Microsoft Ignite 2024
Microsoft Ignite 2024 showcased groundbreaking advancements across security, hybrid work, and cloud management. From the Windows Resiliency Initiative and its Quick Machine Recovery feature to Microsoft Purview’s expanded Data Loss Prevention capabilities, this year’s Ignite highlighted how Microsoft is reshaping IT landscapes. The integration of Windows 365 Link, Universal Print Anywhere, and enhanced Intune features…
-
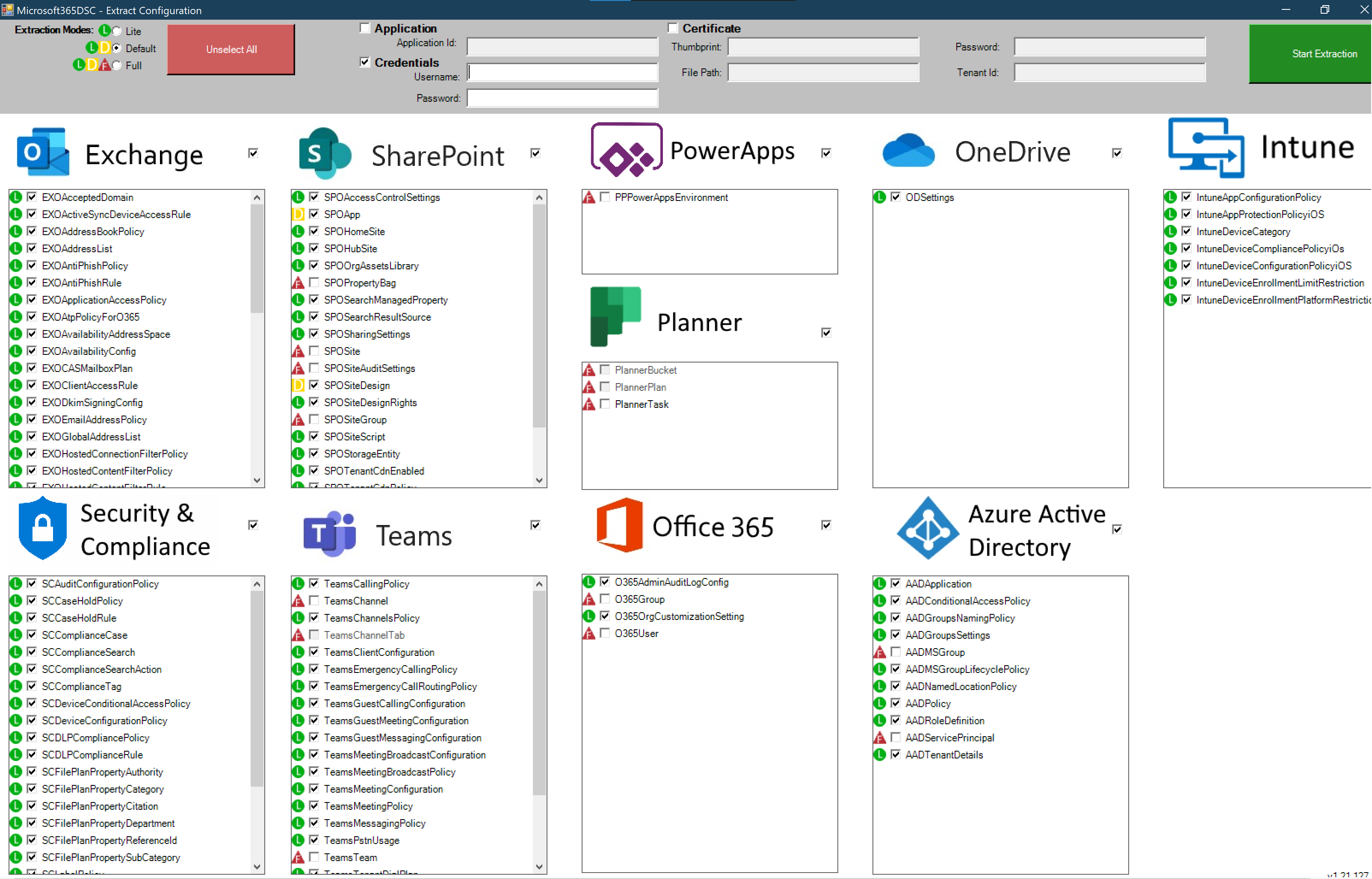
Microsoft 365 DSC: Automate, Configure, and Monitor Like a Pro
Discover how Microsoft 365 Desired State Configuration (DSC) empowers IT professionals to automate, monitor, and maintain tenant configurations with ease. This blog dives into the benefits of DSC, including drift prevention and multi-tenant synchronization, while providing a step-by-step guide for deployment. Learn from real-life examples covering Exchange Online, Intune, and Entra, and explore additional resources…
-

Comprehensive Guide to Setting Up Microsoft Entra Global Secure Access (GSA) with Internet Access, Licensing, and Key Differences with SSE
Learn how to implement Microsoft Entra Global Secure Access (GSA) for secure internet access. This step-by-step guide covers everything from activating GSA for your tenant to configuring web content filtering, security profiles, and conditional access policies. Understand the key differences between GSA and Security Service Edge (SSE) and how to improve your organisation’s security posture.…
